PolyShell attacks target 56% of all vulnerable Magento stores
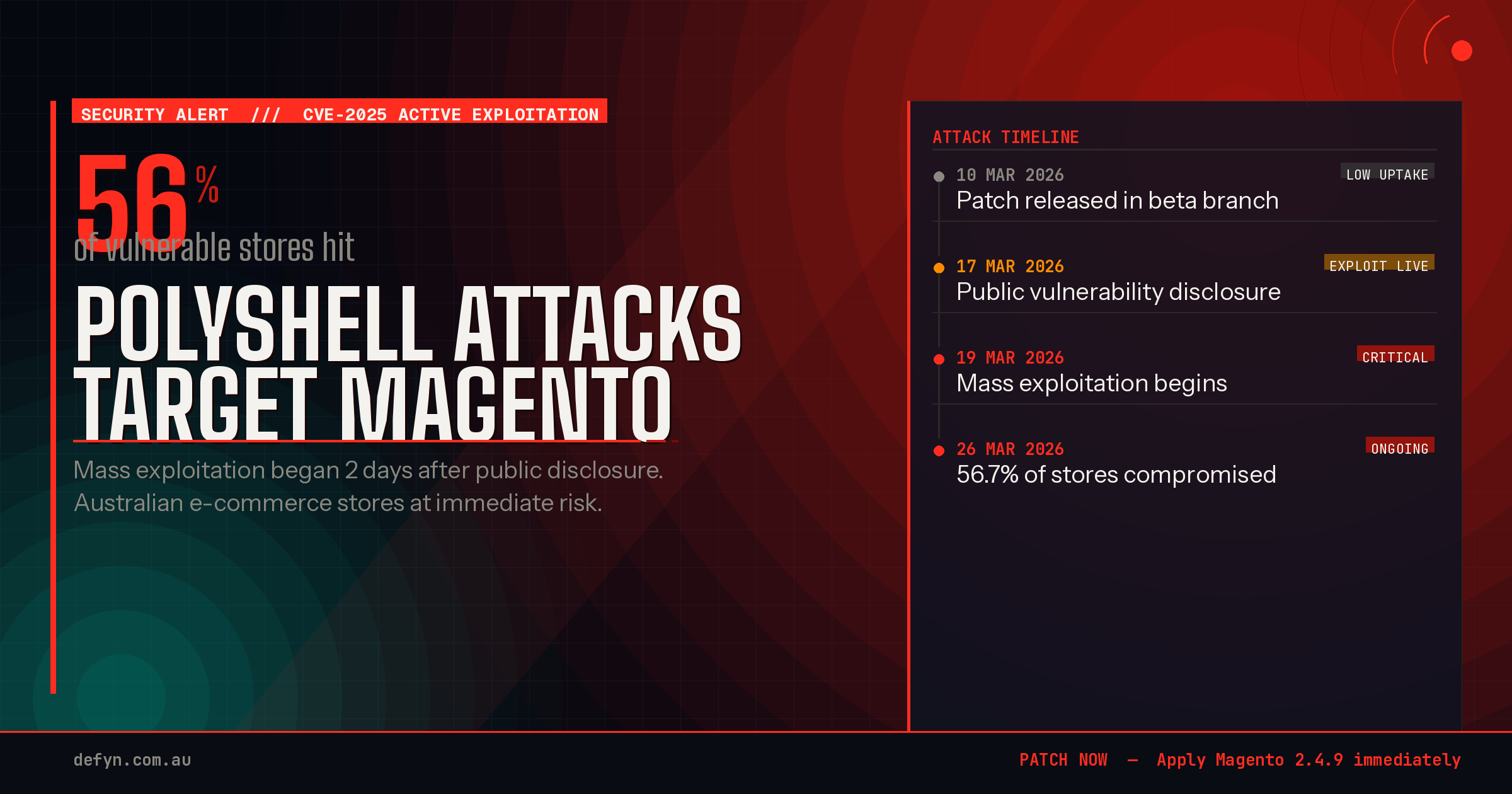
Table of Content
Imagine waking up to find your online store gone. The one you built with so much effort. Your customers’ payment details stolen. Your reputation ruined. This is the nightmare for thousands of store owners now.
We’ve been watching this with growing concern. On 19 March, just two days after it was made public, polyshell exploitation started. It hit Magento Open Source and Adobe Commerce version 2 installations worldwide. The speed was both breathtaking and terrifying.
Security researchers at Sansec have confirmed the scale of this magento security vulnerability. They found that polyshell attacks hit 56.7% of all vulnerable stores. That’s more than half. If your Magento store hasn’t been patched, the odds aren’t in your favour.
These magento malware attacks aren’t slowing down. They’re happening right now, on every continent. Australian retailers are at risk. We wanted to explain this clearly, honestly, and with steps you can take today.
Key Takeaways
- Polyshell exploitation began on 19 March 2025, targeting Magento Open Source and Adobe Commerce version 2 stores globally.
- Sansec confirmed that 56.7% of all vulnerable stores have been hit by this magento security vulnerability.
- Attacks started just two days after the vulnerability was publicly disclosed, giving store owners almost no reaction time.
- These magento malware attacks are currently ongoing and show no signs of stopping.
- Australian e-commerce stores running unpatched Magento installations face significant and immediate risk.
- Prompt patching and security monitoring are essential to protect your store and your customers’ data.
Understanding the PolyShell Magento Security Vulnerability
The PolyShell exploit is a major threat to Adobe Commerce security. It targets the REST API, turning it into a backdoor for attackers. This is a big problem for Australian store owners.
What Makes PolyShell Different from Previous Exploits
PolyShell uses polyglot files, which are valid in multiple formats. This means a single file can be an image and a PHP script at the same time. Traditional scanners miss these files because they look normal.
Old exploits used known weaknesses or outdated parts. PolyShell is different because it uses a trusted process. Without the latest security patches, stores are at risk.
The REST API Connection and File Upload Weakness
Magento’s REST API lets users upload files for custom cart options. Attackers use this to upload polyglot files. If the server settings allow it, the malicious code runs without being stopped.
This makes unpatched stores very vulnerable. The attack doesn’t need admin credentials, making it easier to exploit.
Remote Code Execution and Account Takeover Risks
Once a polyglot file is uploaded, attackers have two main ways to attack:
- Remote code execution (RCE) — full server control
- Account takeover via stored XSS — taking over admin and customer sessions
| Risk Type | Attack Method | Severity | Mitigated by Patches |
|---|---|---|---|
| Remote Code Execution | Polyglot PHP file via REST API | Critical | Yes |
| Stored XSS | Malicious script in uploaded file | High | Yes |
| Account Takeover | Session hijacking through XSS | High | Yes |
| Data Exfiltration | Server access post-RCE | Critical | Partial |
We urge all Australian retailers to fix these security issues quickly. Applying the latest security patches is the most important step you can take now.
Timeline of the Mass Exploitation Campaign
The attack campaign caught many Australian store owners by surprise. We’ve seen how ecommerce platform vulnerabilities in Magento were used quickly after public disclosure. This left thousands of shops worldwide exposed.
Adobe released a fix in Magento version 2.4.9-beta1 on 10 March 2026. But, this patch was in a beta branch. So, most production stores hadn’t applied it yet. Just two days after the flaw was publicly disclosed on 17 March, attackers launched a mass exploitation campaign on 19 March 2026.
Security firm Sansec tracked the rapid spread in real time. In the first week, the campaign had compromised most vulnerable Magento installations. Attackers used magento sql injection exploits to get in, then escalated their access through the REST API weakness.
Here’s how the campaign unfolded:
| Date | Event | Impact |
|---|---|---|
| 10 March 2026 | Adobe releases patch in version 2.4.9-beta1 | Limited uptake — beta branch only |
| 17 March 2026 | Public disclosure of vulnerability details | Exploit code becomes available to attackers |
| 19 March 2026 | Mass exploitation campaign begins | Automated scanning targets unpatched stores |
| 26 March 2026 | Sansec reports 56% of vulnerable stores hit | Majority of exposed Magento shops compromised |
The gap between patch availability and stable release was dangerous. Attackers used this delay to exploit ecommerce platform vulnerabilities. Many retailers running Magento didn’t know about the beta-only fix or waited for a stable release.
This timeline shows just how quickly magento sql injection exploits can cause damage. Knowing these dates helps us prepare for what Australian retailers are facing now.
How Hackers Are Targeting Australian E-commerce Stores
Australian online stores are being targeted by PolyShell hackers. We’ve been watching their moves closely. The patterns show a worrying trend for local businesses. To keep Magento stores safe, we need to know how these hackers work and why they’re a big risk for us.
IP Addresses and Scanning Patterns We’ve Identified
Sansec found a list of IP addresses scanning for Magento vulnerabilities. These scans are not random. Hackers use tools to find store versions and look for open doors.
Here’s what we’ve seen in attacks on Australian stores:
- Automated REST API probes hitting stores during off-peak AEST hours
- Rapid sequential scanning of multiple domains hosted on the same server
- Targeted file upload attempts within minutes of identifying a vulnerable endpoint
- Reconnaissance activity originating from rotating IP addresses across multiple regions
| Attack Pattern | Frequency (AU Stores) | Risk Level |
|---|---|---|
| REST API vulnerability scanning | Up to 200 probes per day | Critical |
| Malicious file upload attempts | 50–80 attempts per day | Critical |
| Admin panel brute force | 100–150 attempts per day | High |
| Payment skimmer injection | 10–30 attempts per day | Critical |
Why Australian Retailers Are Particulary at Risk
Many Australian e-commerce sites run older Magento versions. Not patching quickly is a big problem. Smaller teams often don’t have enough security staff, so updates can be delayed for weeks or months.
Time zone differences also play a part. Patches from Adobe in the US may not reach Australian teams until the next day. Keeping up with security updates is now essential for survival.
The Novel WebRTC Payment Card Skimmer Attack
In 2024, a new payment card skimmer attack has been spotted. It uses Web Real-Time Communication (WebRTC) to steal card data. This is a big problem for Australian store owners already facing magento zero-day vulnerabilities.
How WebRTC Technology Bypasses Traditional Security
WebRTC is a browser feature for voice and video calls. Now, attackers use it to send stolen payment details. They do this through DTLS-encrypted UDP connections, avoiding standard web requests.
They connect to a server using WebRTC, bypassing normal checks. Security scanners won’t catch it because it doesn’t use HTTP.
DTLS-Encrypted UDP vs Standard HTTP Traffic
| Feature | Standard HTTP Exfiltration | WebRTC DTLS-Encrypted UDP |
|---|---|---|
| Protocol | HTTP/HTTPS (TCP) | DTLS over UDP |
| CSP Blocked | Yes | No |
| Visible in Network Logs | Easily detected | Blends with media traffic |
| Encryption | TLS (inspectable via proxy) | End-to-end DTLS (harder to inspect) |
| Detection Difficulty | Low | Very High |
The Lightweight JavaScript Loader Mechanism
The attack starts with a small JavaScript loader. It’s injected through magento zero-day vulnerabilities. This loader gets a second payload over WebRTC, avoiding CSP.
The skimmer waits to run, using requestIdleCallback. It only acts when the browser is idle. Australian retailers need to check for these attacks to protect customer data.
Adobe’s Response and Current Security Patches Status
Adobe has acknowledged the security issues with PolyShell in Adobe Commerce. But, their response has left many Australian store owners worried. On 10 March 2026, Adobe released a fix in version 2.4.9-beta1. The problem is, this update is in the beta branch, not the stable production channel.
This leaves most Magento stores running on production versions at risk. BleepingComputer asked Adobe when they would release patches for stable versions. Adobe hasn’t replied yet.
This delay is concerning for our Australian clients. Every day without a patch is another day attackers can use the REST API weakness. They can install skimmers without being detected.
“Patching delays in e-commerce platforms can cost retailers millions in fraud losses and erode hard-won customer trust.”
Here’s a quick snapshot of where things stand right now:
| Version | Patch Status | Suitable for Production | PolyShell Risk Level |
|---|---|---|---|
| Magento 2.4.9-beta1 | Fix included | No — beta only | Low (if applied in staging) |
| Magento 2.4.8 (stable) | No patch released | Yes — current production | Critical |
| Magento 2.4.7-p4 (stable) | No patch released | Yes — current production | Critical |
| Magento 2.4.6-p9 (stable) | No patch released | Yes — current production | Critical |
We urge store owners to check Adobe’s security bulletin page every day. Until official patches are released for stable branches, it’s essential to follow the protective measures we suggest. This will help protect against the exploitation of these security flaws.
Protecting Your Magento Store from PolyShell Attacks
To keep your Magento store safe, you need a strong defence plan. PolyShell is targeting many sites, so it’s urgent for Australian store owners to take action. Applying security updates is a good start, but there’s more to do.

Immediate Security Measures We Recommend
Here are some key steps to take right now:
- Install the latest security updates magento 2 patches from Adobe.
- Check your REST API endpoints for any suspicious file uploads.
- Look at your cart item custom options for unexpected code.
- Limit admin panel access to trusted IP addresses only.
- Turn on two-factor authentication for all backend accounts.
Content Security Policy Configuration Best Practices
A strong Content Security Policy (CSP) is vital for your store’s safety. The new WebRTC-based skimmer can get past some connect-src rules. So, your CSP needs careful attention.
| CSP Directive | Recommended Setting | PolyShell Protection Level |
|---|---|---|
| script-src | self only, no unsafe-inline | High |
| connect-src | Whitelist specific domains | Moderate (WebRTC bypass risk) |
| default-src | self with strict fallback | High |
| frame-src | none or trusted payment gateways | High |
Monitoring for Indicators of Compromise
Sansec has shared indicators of compromise (IoCs) to watch for. Use these in your monitoring tools. Look for unknown PHP files in your webroot and any UDP traffic that might mean data is being sent out.
A single missed patch can open the door to full remote code execution — proactive monitoring is not optional.
Do regular security checks to find and fix weak spots before hackers do. Keeping up with Magento 2 security updates is the best way to protect your store.
Impact on Major E-commerce Platforms and Enterprises
We often think big companies with lots of money are safe from hackers. But the PolyShell campaign shows this isn’t true. Ecommerce platform vulnerabilities affect all, no matter the size or income.
A global car manufacturer worth over $100 billion was hit hard. Security experts at Sansec found a payment card skimmer on their website. Despite warnings, the company didn’t act. This left customer payment data at risk for a long time.
The 56.7% infection rate in vulnerable Magento stores is shocking. It doesn’t matter if you’re a small Aussie shop or a big global brand. Magento SQL injection attacks can harm your store just the same. Hackers use tools that don’t care about your income before they attack.
| Business Size | Perceived Risk Level | Actual Risk Level | Common Gap |
|---|---|---|---|
| Small retailers (under $1M revenue) | High | High | Limited patching resources |
| Mid-market ($1M–$50M revenue) | Moderate | High | Delayed security updates |
| Enterprise ($50M+ revenue) | Low | High | Complex approval workflows slow patching |
Big companies face a special challenge. Their big systems and slow change processes make them vulnerable. Hackers use Magento SQL injection attacks before they can patch up.
Big breaches in e-commerce can be disastrous. They can leak millions of customer records and lead to big fines. The damage to a company’s reputation can cost much more than any security measures.
Speed of response matters more than the size of your security team.
In the next section, we’ll talk about how our team helps Magento store owners in Australia. We support all, from small shops to big operations.
What We’re Doing to Help Australian Magento Store Owners
Facing threats like PolyShell can be very stressful. Australian online stores need a team that really understands their market. We’ve created services to tackle every Magento security issue, from finding the problem to fixing it.

Our Security Assessment Services
Our team does detailed security checks for Australian Magento sites. We look for all kinds of threats, including PolyShell. Each check gives you a clear plan of what to do next.
Here’s what our assessment covers:
- Full scan for known and new PolyShell threats
- Review of REST API setup and access control
- Check for patch gaps against Adobe’s latest security updates
- Advice on making your Content Security Policy stronger
- Search for WebRTC skimmers in payment areas
We help with applying patches and making your site more secure. Our advice is practical and fits your store’s needs.
Emergency Response Support for Compromised Stores
If your store has been hacked, time is of the essence. Our emergency team is ready to act fast. We’ll stop the threat, remove bad code, and make your site safe again quickly.
Call us at hello@defyn.com.au if you’re dealing with Magento issues or your current developer can’t fix the security problem.
Keeping your customers’ data safe and your brand’s reputation is our main goal. Whether you need a regular check or urgent help after an attack, we’re here to support you.
Conclusion
The PolyShell threat is a serious issue for Magento store owners. With 56.7% of vulnerable installations already hit, it’s one of the most aggressive campaigns we’ve seen. The danger comes from REST API exploitation, remote code execution, and a new WebRTC skimmer.
We urge every Australian e-commerce business running Magento to act fast. Check your security settings, apply Adobe patches, and set up strong Content Security Policies. Also, keep an eye out for any signs of compromise. Waiting is risky, as attacks are scanning and exploiting stores on a large scale.
If your store has been hit or you need help securing it, our team is here for you. Contact us at hello@defyn.com.au for a security check, emergency support, or customisation help. We’re dedicated to protecting Australian retailers from this threat and any future variants.










